Preventing Malware from Spreading in Network Devices
Malware has become a significant threat to network security, with various types and methods of spreading. As soon as malware infiltrates one device, the potential for it to spread to others within the same network is a pressing concern. This comprehensive guide explores proactive strategies and best practices to prevent the spread of malware in network devices, reducing the risk of data breaches and cyber attacks.
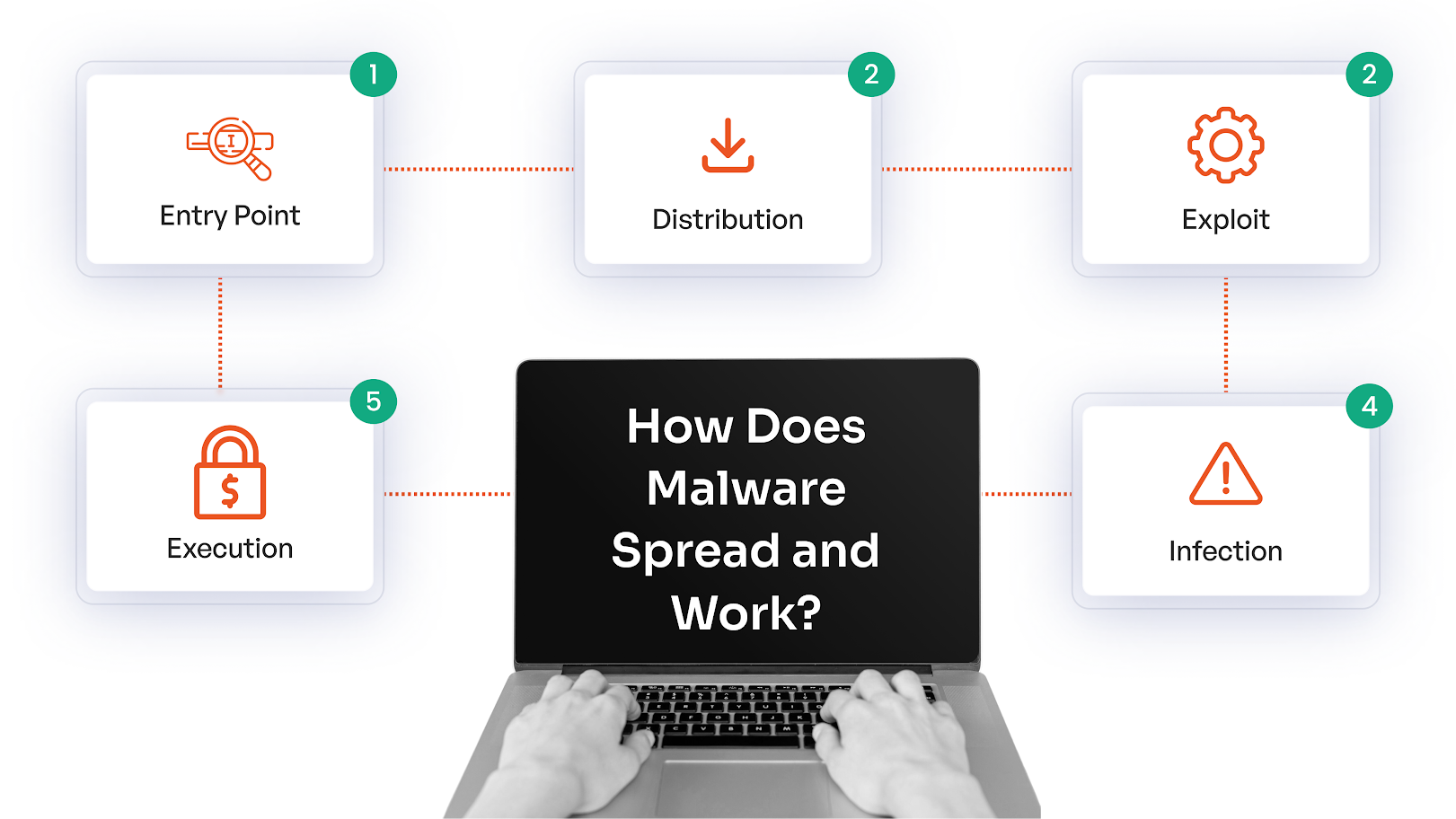
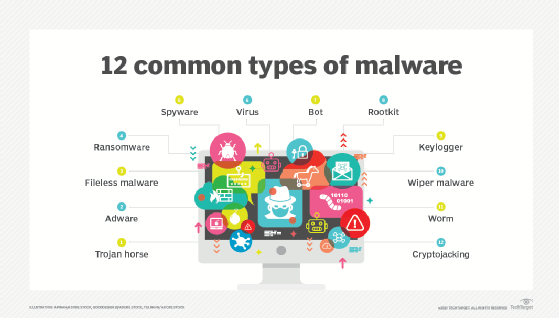
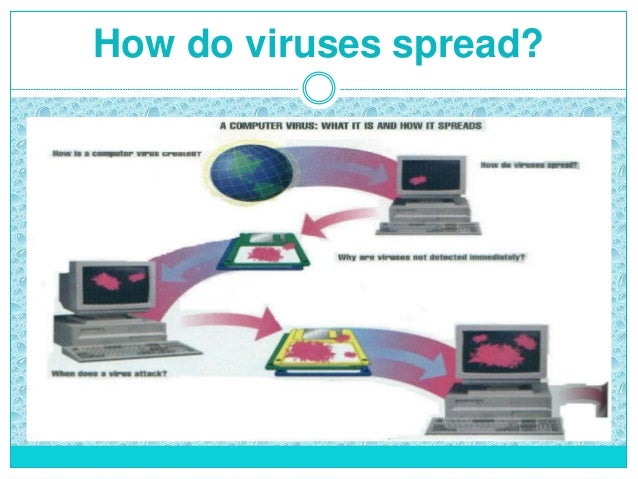
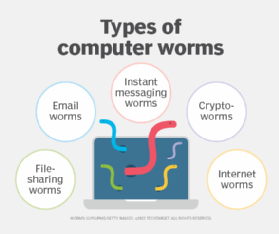
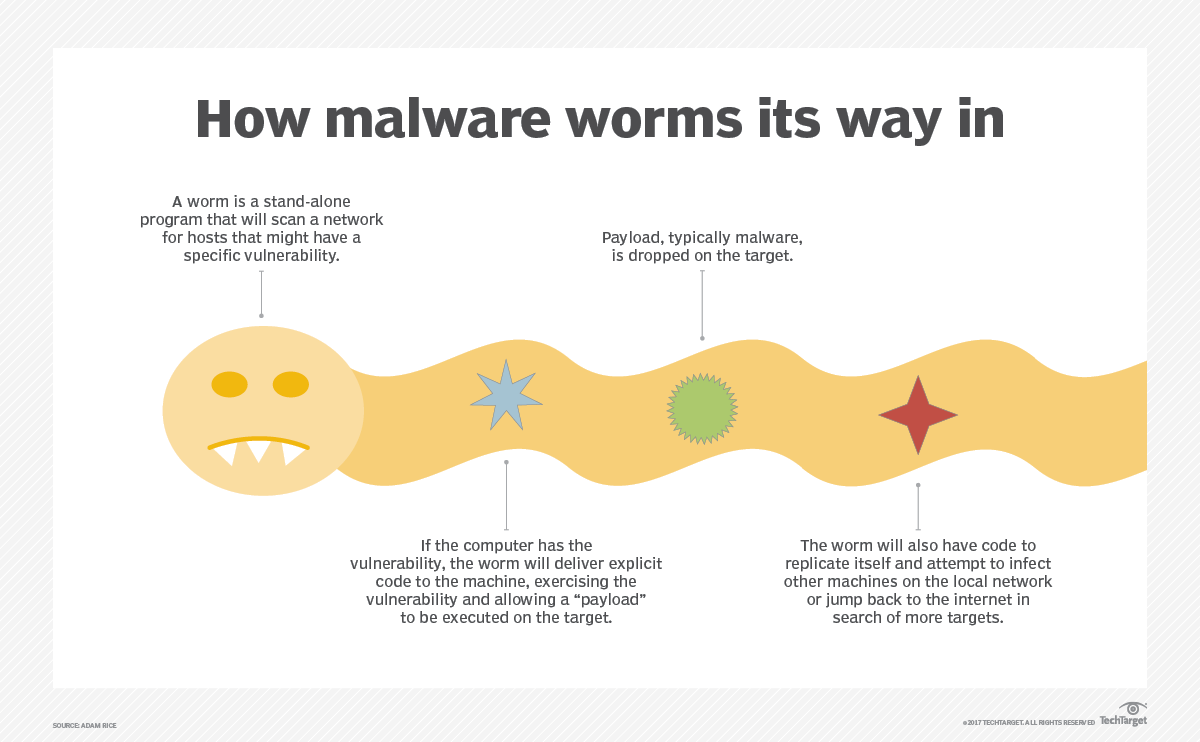
Malware is unwanted software designed by malicious actors to infiltrate devices or spread across networks, with a typical end goal to disrupt systems, steal data, or obtain financial payouts. Malware can spread mainly through hacked sites, malicious downloads, risky email attachments, and other channels. It can harm devices and data by stealing information, encrypting or deleting files, spying on activities, or hijacking system functions.
Prevention Measures
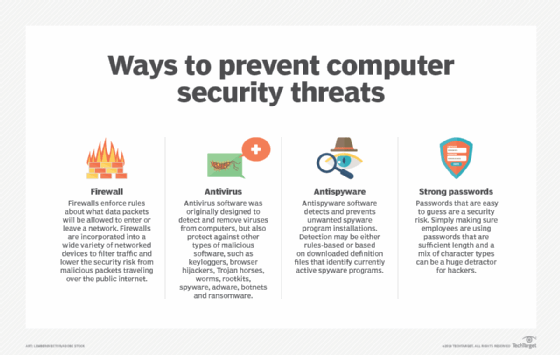
Preventing malware from spreading in network devices requires a comprehensive approach that includes technical measures, such as firewalls and antivirus software, as well as employee education and awareness. Here are some key prevention measures to consider:
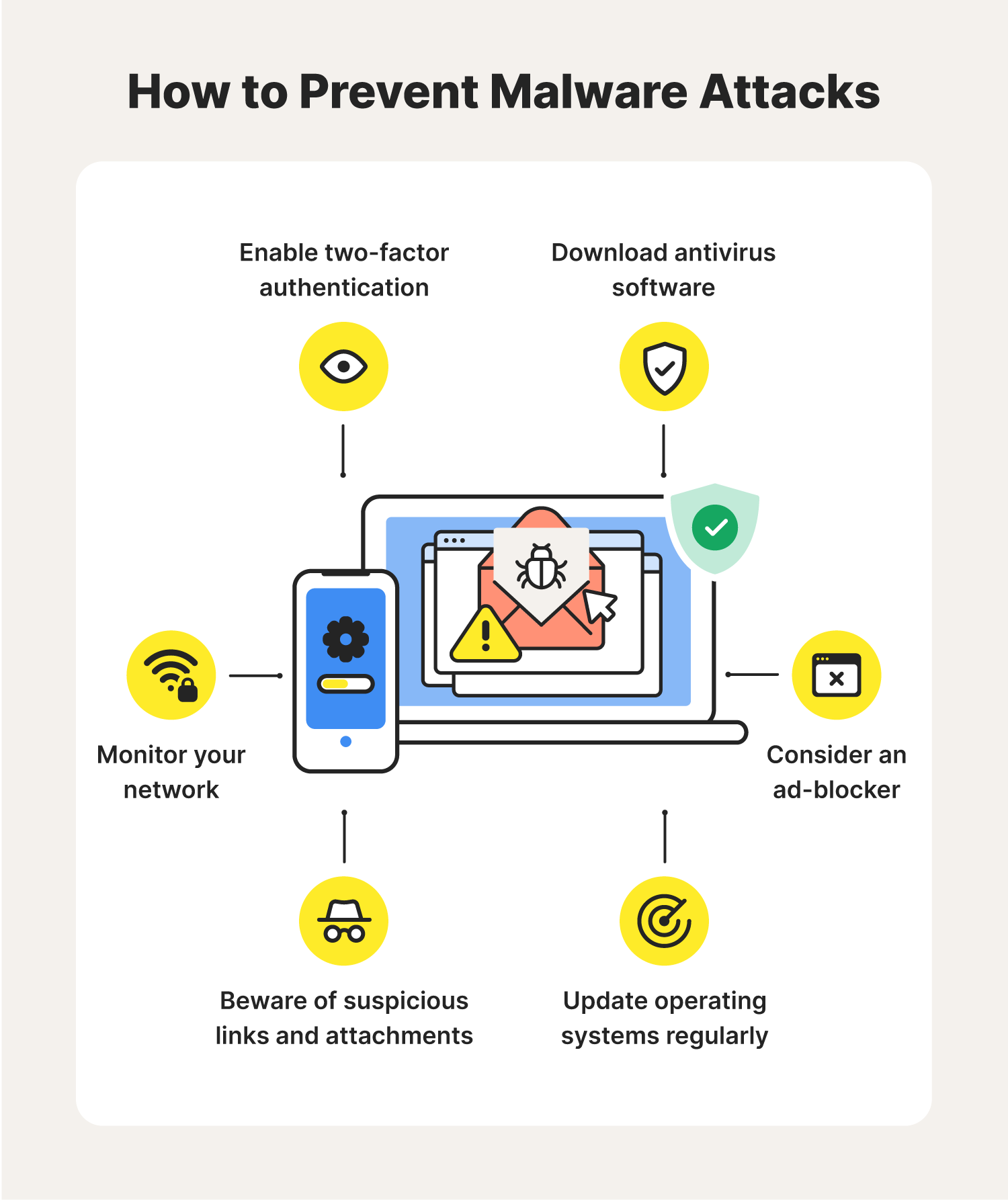
- Install antivirus software on all devices connected to your network, and configure firewalls to block suspicious traffic. This will help detect and prevent malware from spreading.
- Avoid suspicious emails, links, and attachments, and never download software from untrusted sources.
- Regularly update your operating system, software, and applications to patch security vulnerabilities.
- Use strong, unique passwords, and enable two-factor authentication to prevent unauthorized access.
- Use a VPN (Virtual Private Network) to encrypt internet traffic and protect your devices from public Wi-Fi threats.
- Segment your network to prevent lateral movement and contain malware within a smaller scope.
- Monitor network activity and implement a robust incident response plan.

Moving forward, it's essential to keep these visual contexts in mind when discussing Preventing Malware From Spreading In Network Devices.
Containment and Eradication
In the event of a malware outbreak, it is essential to contain and eradicate the malware to prevent further spread. Here are some steps to take:
- Isolate infected devices from the network to prevent malware from spreading.
- Run antivirus scans on all affected devices to identify and remove malware.
- Disconnect from the internet and any other network connections to prevent malware from communicating with its Command and Control (C2) server.
- Use a reputable antivirus software to scan and remove malware, and update the software regularly.
- Restore backups from a known clean state and re-image devices if necessary.
Best Practices
To prevent malware from spreading in network devices, follow these best practices:

- Conduct regular security audits to identify vulnerabilities and address them proactively.
- Implement a security information and event management (SIEM) system to monitor network activity and detect anomalies.
- Establish a incident response plan to guide responses to malware outbreaks and other security incidents.
- Provide regular security training and awareness programs for employees to educate them on malware risks and best practices.
- Use endpoint detection and response (EDR) tools to monitor and respond to endpoint threats.
- Implement network access control (NAC) to limit access to sensitive areas and resources.
Conclusion
Preventing malware from spreading in network devices requires a multi-faceted approach that includes technical measures, employee education, and incident response planning. By following the prevention measures, containment and eradication steps, and best practices outlined in this guide, you can reduce the risk of malware outbreaks and ensure the security and integrity of your network devices.
Final Thoughts
As long as cybercriminals continue to find new and innovative ways to infiltrate networks and devices, malware will always pose a threat. To avoid falling victim to malware attacks or mitigate those that are already on your devices or network, adopting some of the tips above will put you in a far stronger position. Stay vigilant, stay informed, and stay protected.