Protect Yourself from Phishing Threats: Understanding and Encrypting Data
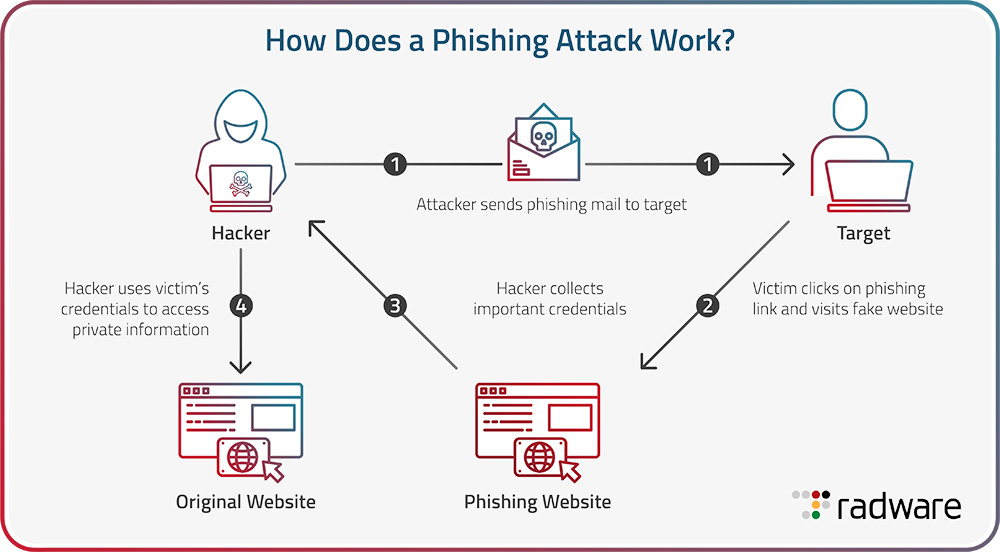
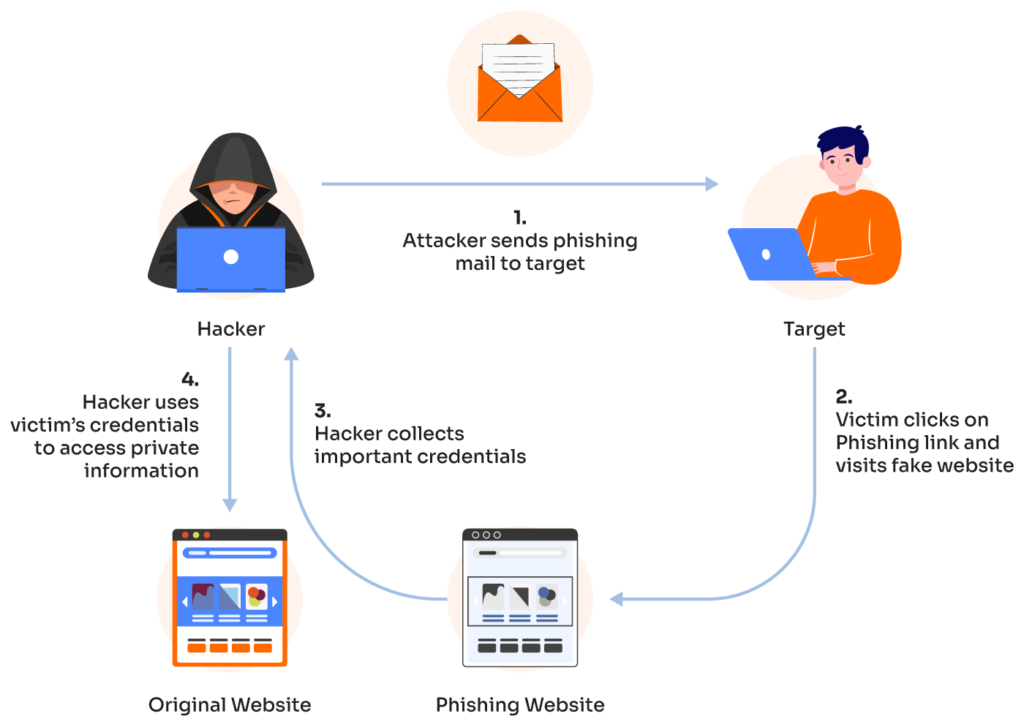
Phishing is the most common and successful type of cyberattack, with scammers attempting to deceive users into divulging sensitive personal information, login credentials, or financial data through fraudulent emails. As organizations and individuals face growing threats from phishing, protecting email communications is a crucial aspect of cybersecurity.
Phishing attacks are a type of cybercrime where scammers pose as legitimate companies or individuals to steal sensitive information such as usernames, passwords, credit card numbers, and other personal details. These attacks typically occur through deceptive emails, text messages, phone calls, and other forms of communication that appear to come from trusted sources.
Encrypting Data from Phishing Threats

This particular example perfectly highlights why Encrypt Data From Phishing Threat is so captivating.
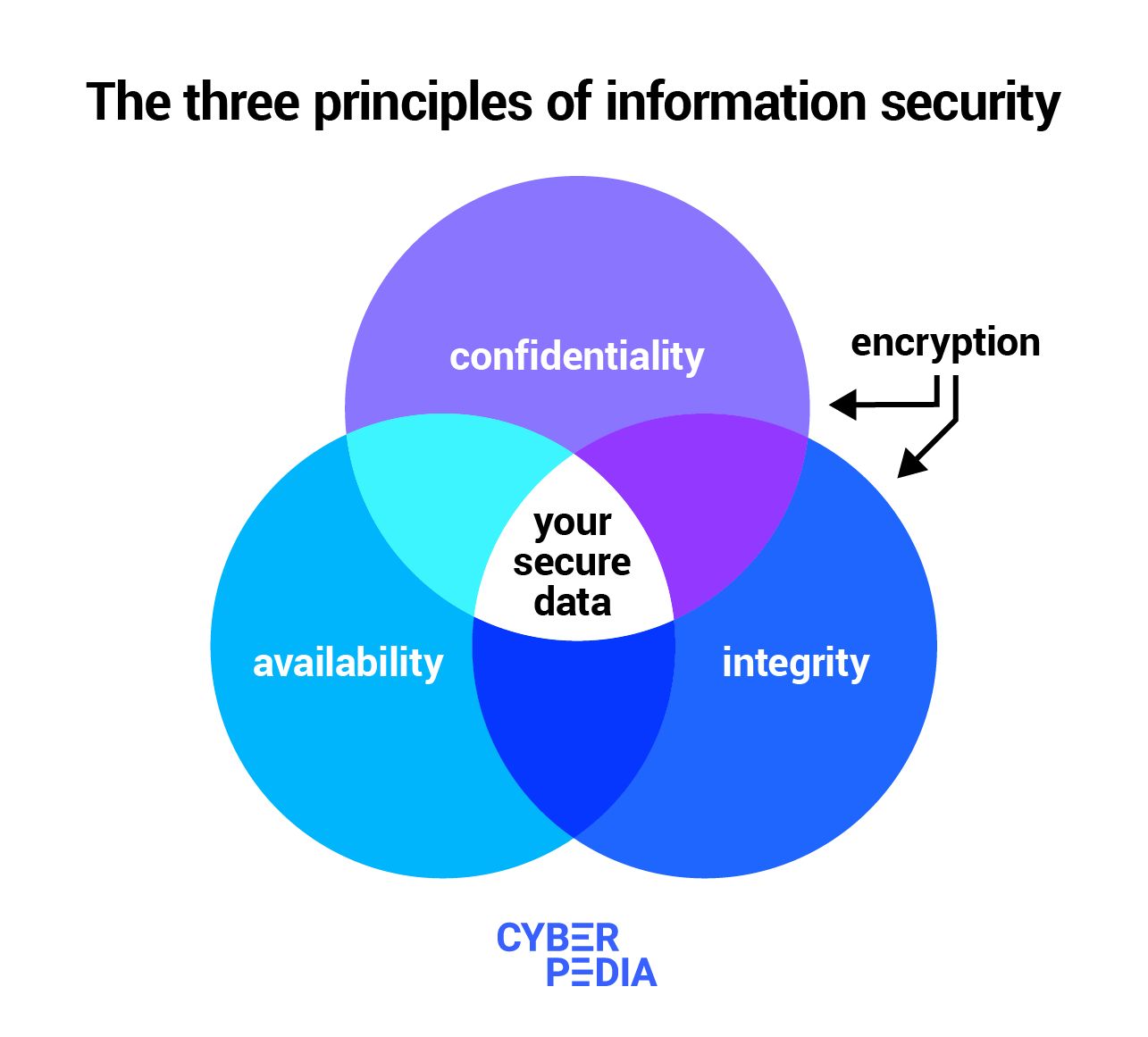
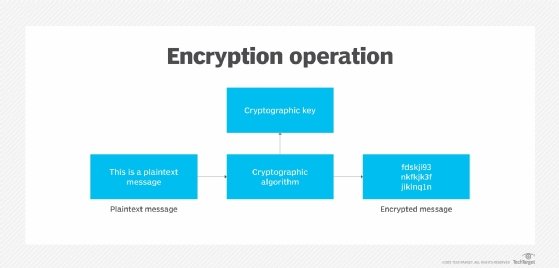
One of the most effective ways to protect yourself from phishing threats is to encrypt your data. Encryption is the process of converting plaintext data into unreadable code, known as ciphertext, using a secret key. This makes it virtually impossible for unauthorized individuals to access the data, even if they manage to obtain the encrypted files.
Encryption programs take the original data, known as plaintext, and a secret key as input and output seemingly random blocks of data, called ciphertext. To recover the plaintext, a decryption program takes the ciphertext and the secret key as input and outputs the original data.
Why Encrypting Data is Essential

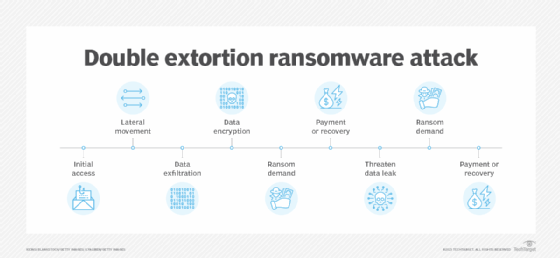
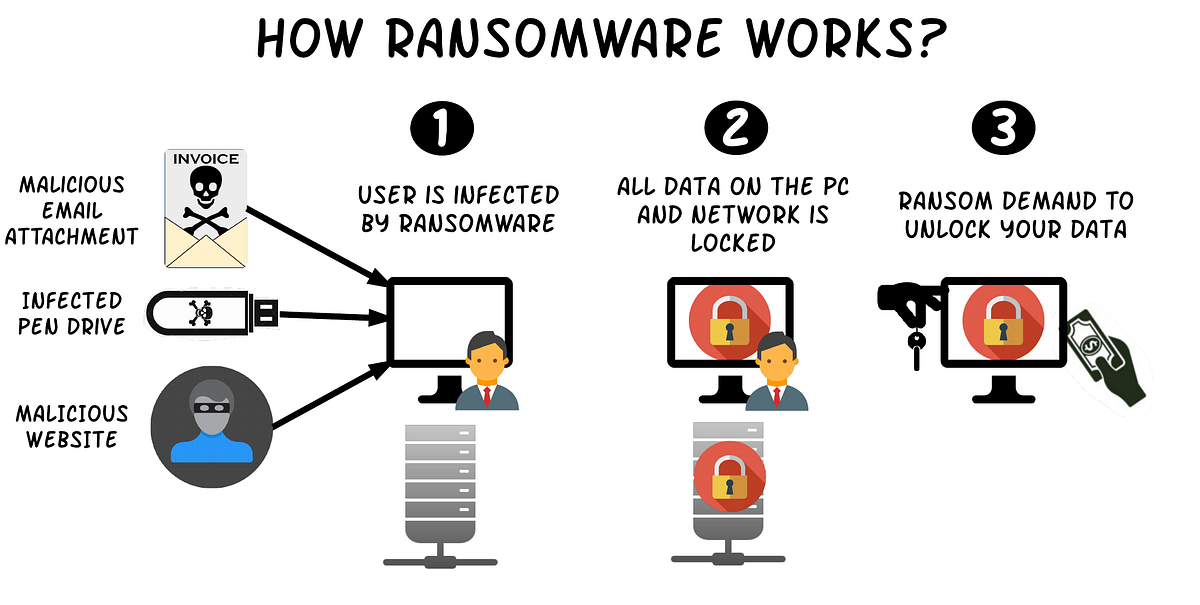
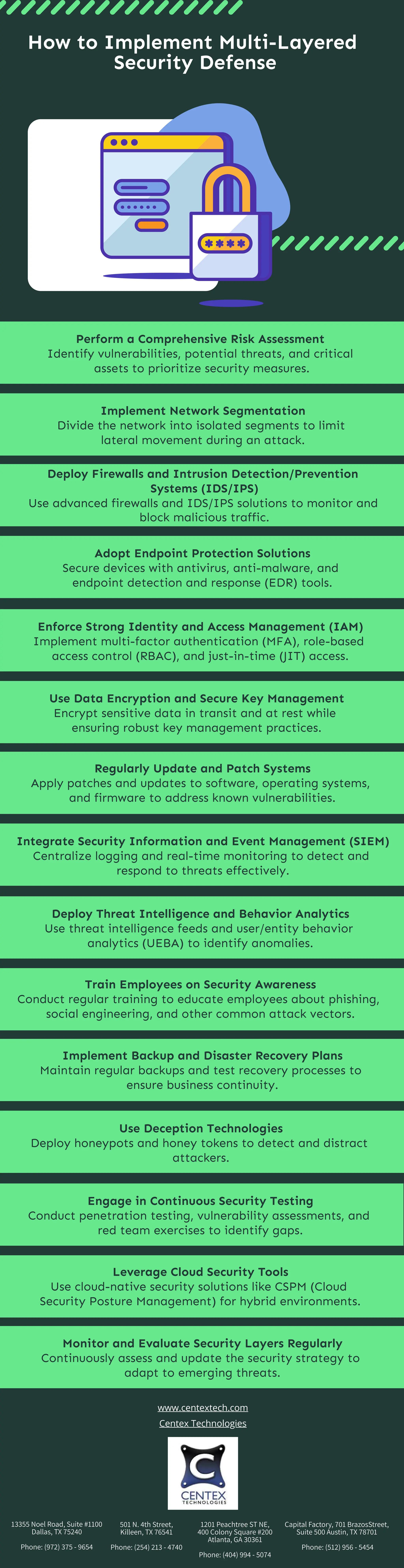
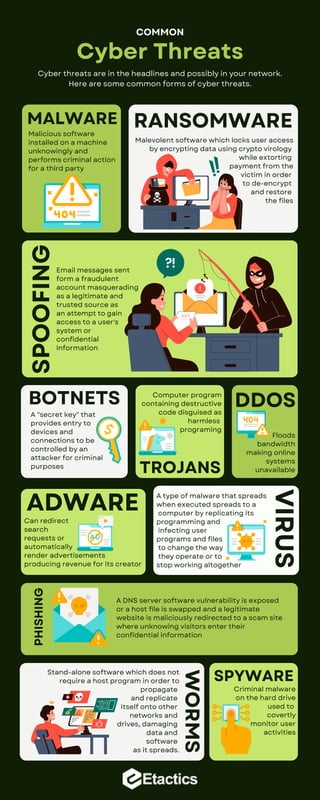
Encrypting data is essential in today's digital landscape where cyber threats are becoming increasingly sophisticated. Phishing attacks are a significant threat because they exploit people rather than technological vulnerabilities. Attackers use tactics like phishing, malware, and ransomware to steal data, disrupt systems, and cause financial loss.
Best Practices for Encrypting Data
To protect yourself from phishing threats, follow these best practices:
Furthermore, visual representations like the one above help us fully grasp the concept of Encrypt Data From Phishing Threat.
- Use strong passwords and enable two-factor authentication: This will make it difficult for attackers to gain access to your accounts, even if they manage to obtain your password.
- Use encryption software**: There are many reliable encryption software available that can encrypt your data, including files, emails, and chats.
- Be cautious with emails and links**: Phishing emails and links can deceive you into divulging sensitive information or installing malware. Be wary of suspicious emails and links, especially if they contain unsolicited content or ask for personal information.
- Use a VPN**: A virtual private network (VPN) can encrypt your internet traffic, making it difficult for attackers to intercept sensitive information.
Key Takeaways
Encrypting data is a critical step in protecting against phishing threats. By understanding how phishing attacks work and taking steps to encrypt your data, you can significantly reduce the risk of cyber threats. Remember, encrypting data is a simple and effective way to safeguard your sensitive information from falling into the wrong hands.
Conclusion
Phishing is a prevalent and damaging type of cyberattack that can compromise your security and reputation. By encrypting your data, using strong passwords, and being cautious with emails and links, you can protect yourself from phishing threats. Remember, data encryption is a crucial step in protecting your sensitive information and safeguarding your digital reputation.