Secure Online Data Transfer: Ensuring the Safety of Your Digital Files
In today's digital age, data transfer has become an essential part of our daily lives. Whether it's to share files, collaborate with colleagues, or simply send large documents, online data transfer has made it easier than ever to share and receive data. However, with this ease comes the risk of data breaches and cyber attacks. In this article, we'll explore the importance of secure online data transfer and provide you with the tools and knowledge to keep your digital files safe.
The Risks of Unsecured Data Transfer
Unsecured data transfer can lead to a range of issues, from data breaches to cyber attacks. When data is transferred online without proper security measures in place, it can be vulnerable to interception by hackers, which can result in the theft of sensitive information. In addition, unsecured data transfer can also lead to data corruption, lost productivity, and reputational damage.

Secure Online Data Transfer Solutions
- TransferNow: A simple, quick, and secure solution to send large files and big documents up to 250 GB per transfer. No registration required.
- Dropbox: A cloud storage service that uses encryption to secure file transfers and access.
- OurTransfers: The fastest and most secure way to share your files, with automatic deletion of files from servers once the transfer has expired.
- Box: A cloud storage service that offers seven permission levels for files and folders, plus link expiration and download restriction capabilities.
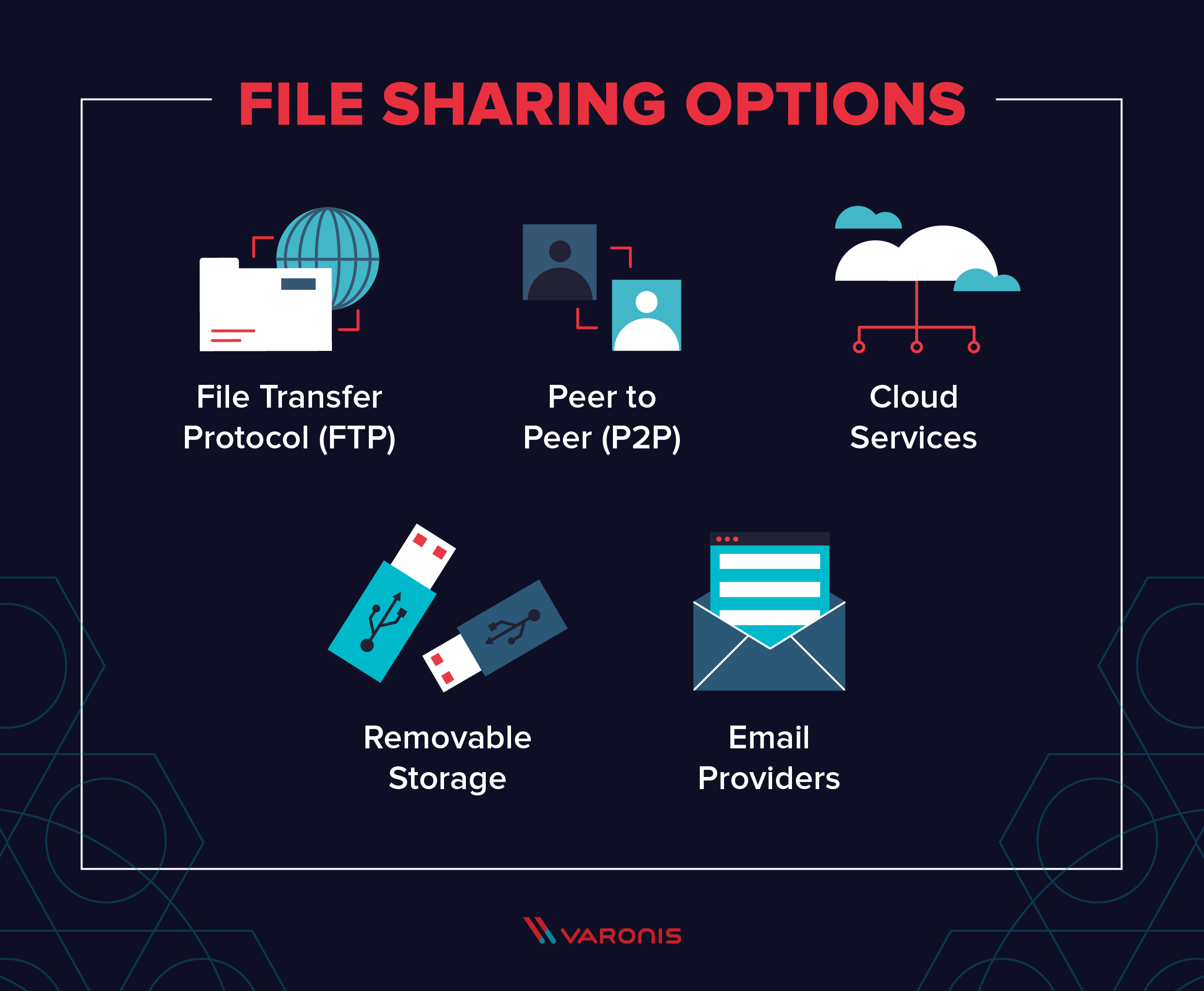
- ShareDrop: A secure and encrypted peer-to-peer connection that transfers information about the file (its name and size) and file data itself.
Features to Look for in Secure Online Data Transfer Solutions

When selecting a secure online data transfer solution, there are several features to look for:
Best Practices for Secure Online Data Transfer
In addition to selecting a secure online data transfer solution, there are several best practices to follow to ensure the safety of your digital files:

This particular example perfectly highlights why Secure Online Data Transfer is so captivating.
- Use Strong Passwords: Use unique and complex passwords to protect your files and accounts.
- Enable Two-Factor Authentication: Add an extra layer of security to your accounts by enabling two-factor authentication.
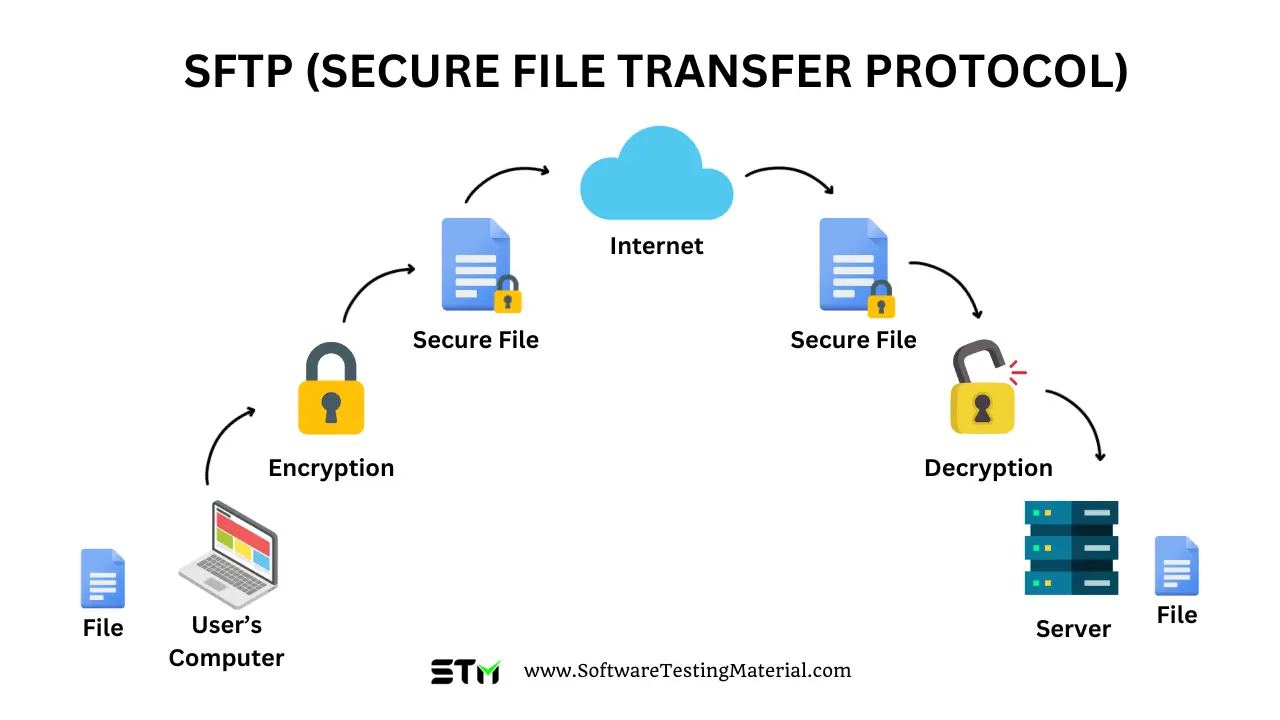
- Use Secure Protocols: Use secure protocols, such as HTTPS and SFTP, to transfer data.
- Regularly Back Up Your Files: Regularly back up your files to prevent data loss in case of a data breach or cyber attack.
Conclusion
Secure online data transfer is essential in today's digital age. By selecting a secure online data transfer solution and following best practices, you can safeguard your digital files and protect yourself against data breaches and cyber attacks. Remember to look for features such as encryption, access controls, automatic deletion, and compliance when selecting a solution, and always stay vigilant and up-to-date on the latest security threats and best practices.