How to Use Encryption to Protect Your Data
Data encryption is a powerful tool for safeguarding sensitive information from unauthorized access. In today's digital age, protecting data has become a top priority for individuals and organizations alike. In this article, we'll delve into the world of data encryption, exploring its basics, types, and best practices. From securing data at rest and in transit to managing encryption keys, we'll cover it all.
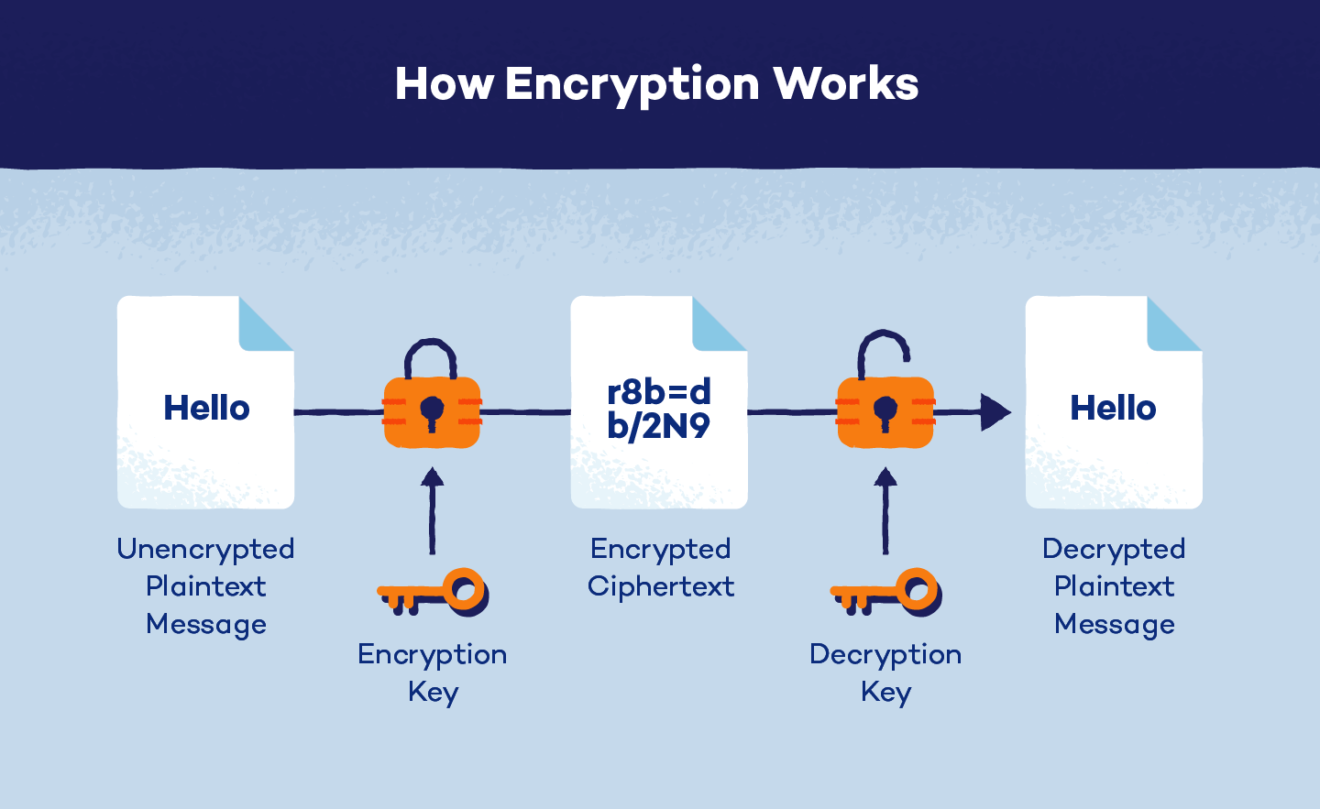
What is Encryption?
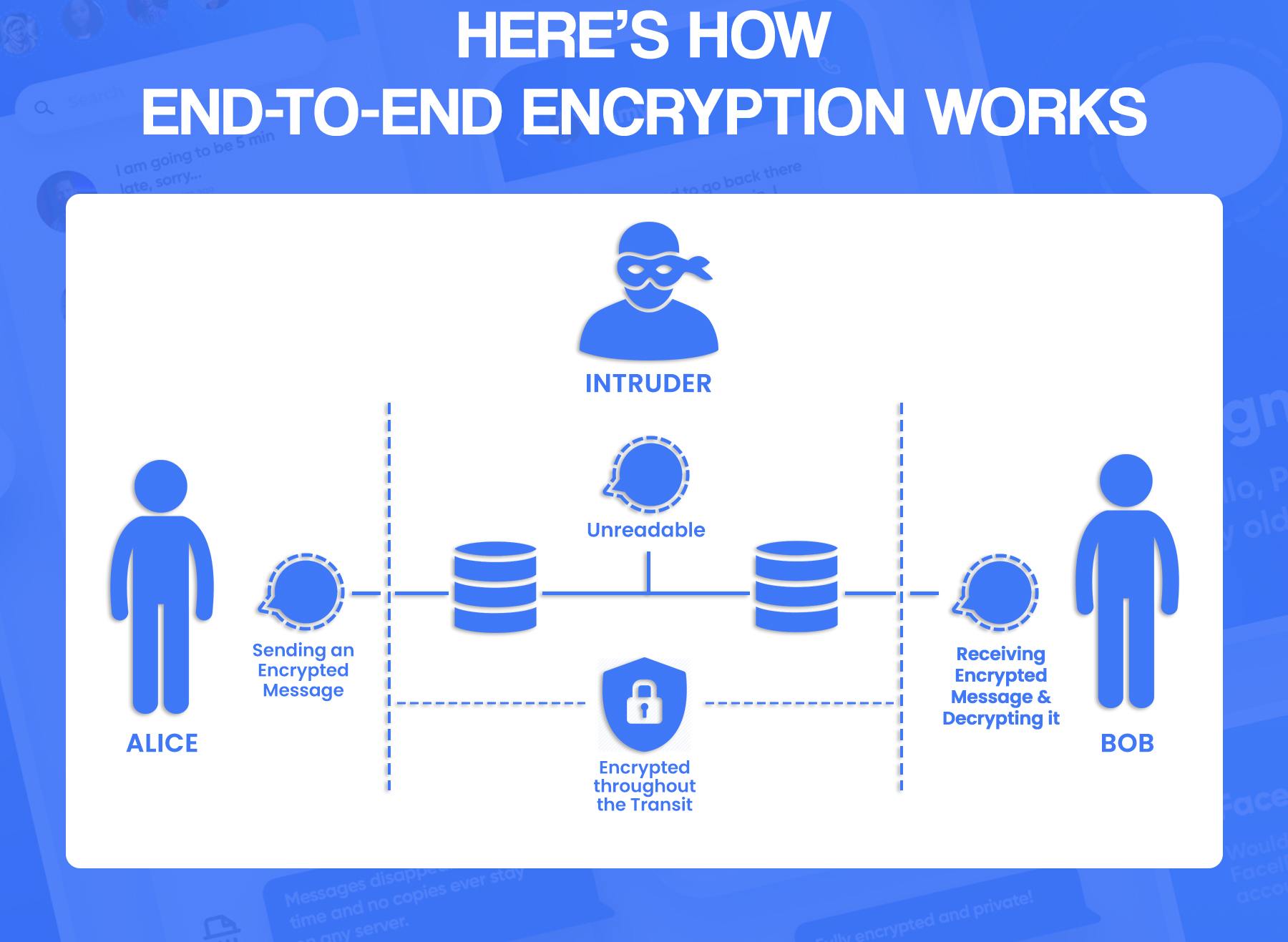
Encryption converts plain text into an encoded format, making it unreadable to anyone without the corresponding decoding key. This process employs cryptographic algorithms to scramble data, ensuring that even if it falls into the wrong hands, it remains inaccessible. Data encryption is a critical component of cybersecurity, providing a robust layer of protection against data breaches and unauthorized access.
Types of Encryption
-
Symmetric Encryption:
Symmetric encryption uses the same key for both encryption and decryption. This approach is fast but requires secure key exchange between parties. Symmetric encryption is commonly used for bulk data encryption.
-
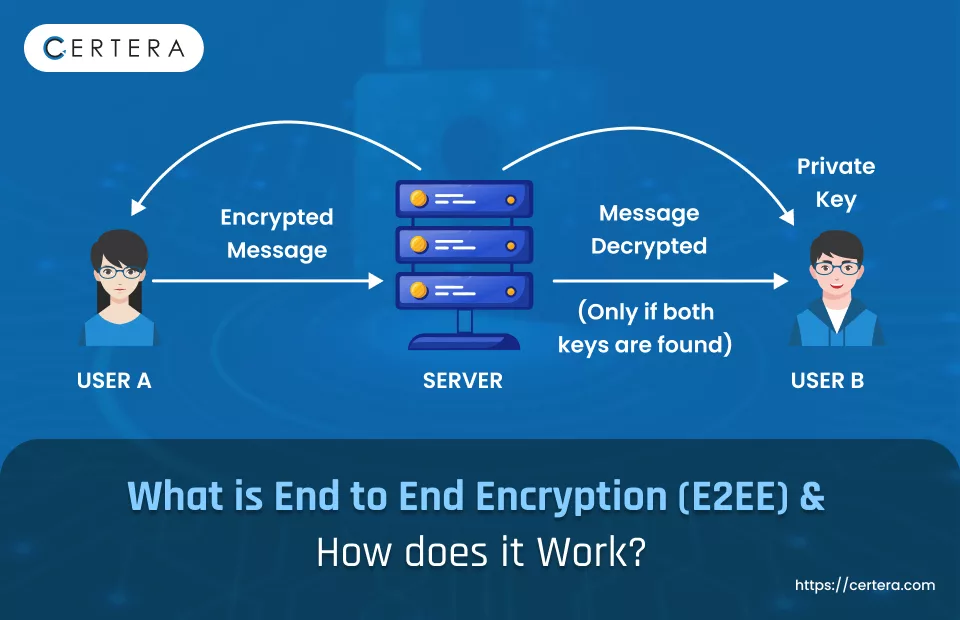
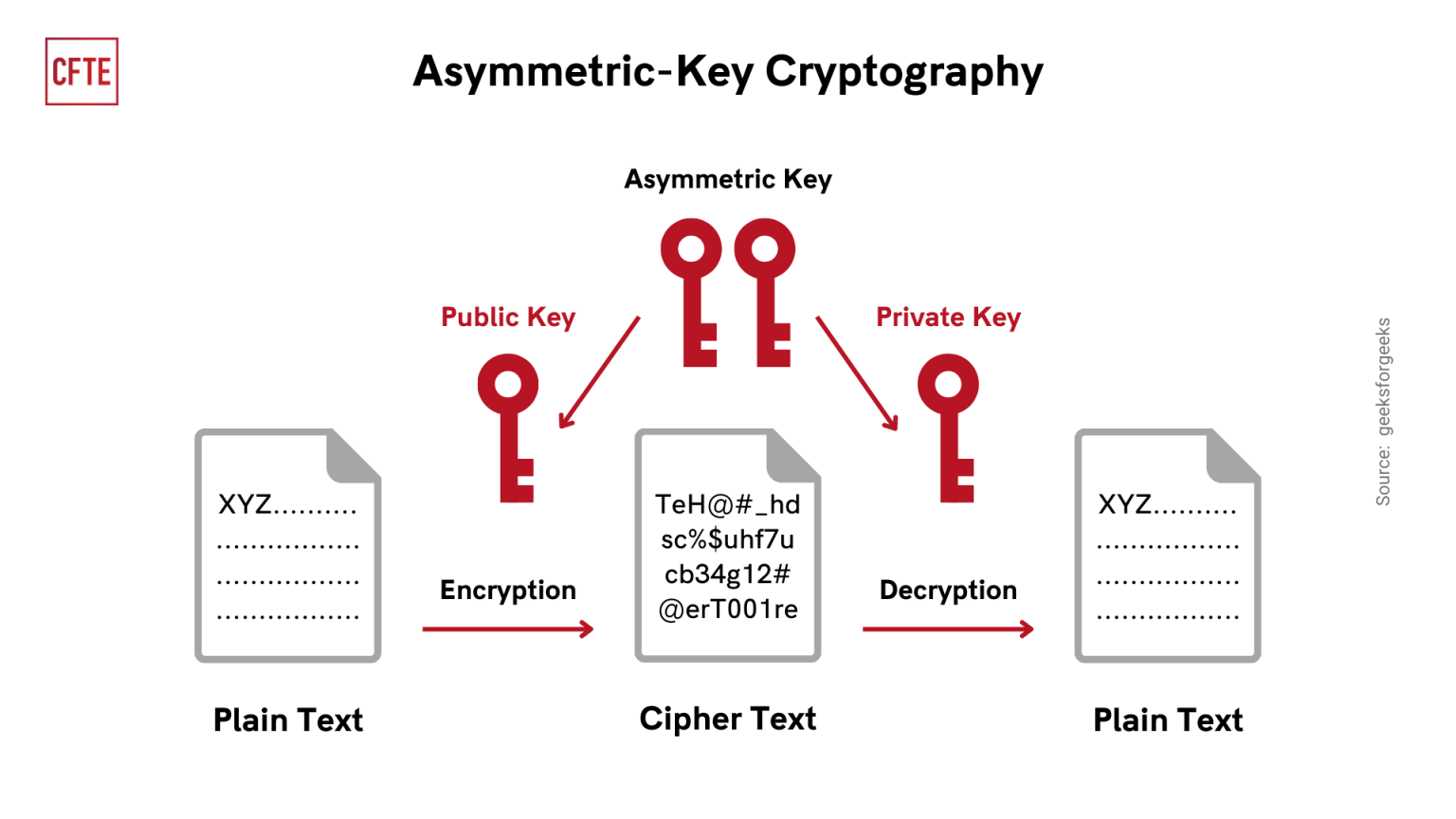
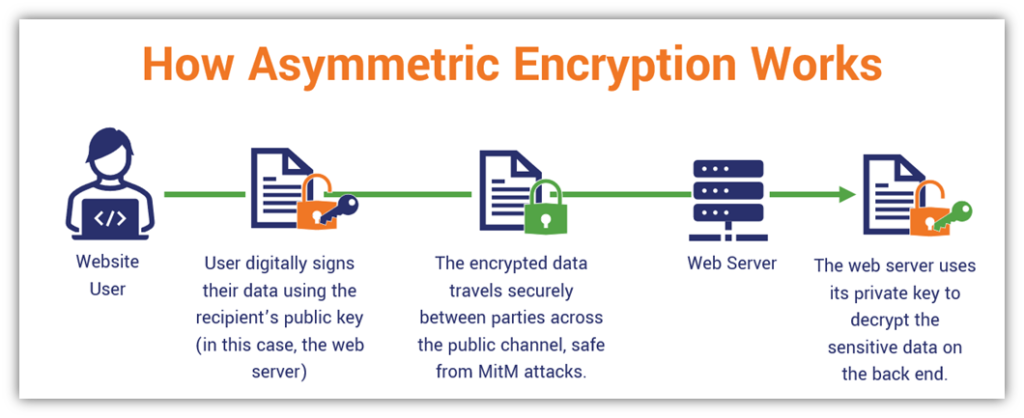
Asymmetric Encryption:
Asymmetric encryption, also known as public-key encryption, uses a pair of keys: a public key for encryption and a private key for decryption. This approach ensures secure key exchange, making it ideal for data transmission.
-
Hash-Based Encryption:
Hash-based encryption uses a one-way hash function to create a digital fingerprint, ensuring data integrity and authenticity.
Choosing the Right Encryption Algorithm

Furthermore, visual representations like the one above help us fully grasp the concept of How To Use Encryption To Protect Your Data.
With numerous encryption algorithms available, selecting the right one can be daunting. Some popular options include:
- Advanced Encryption Standard (AES)
- Elliptic Curve Cryptography (ECC)
- RSA Algorithm
When choosing an encryption algorithm, consider factors like key size, speed, and security requirements.
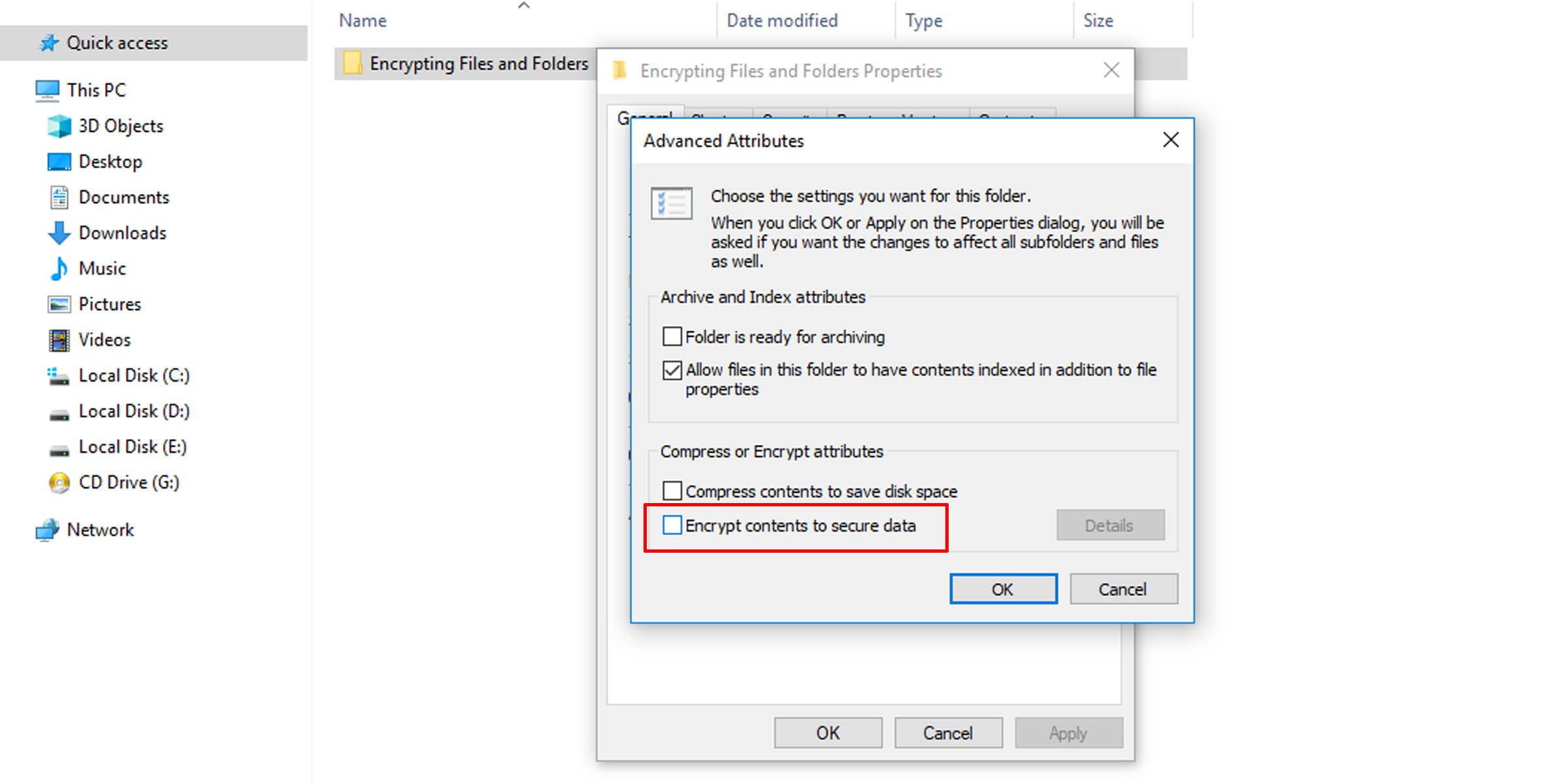
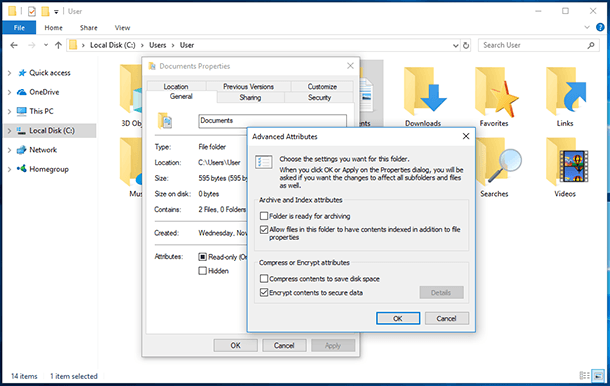
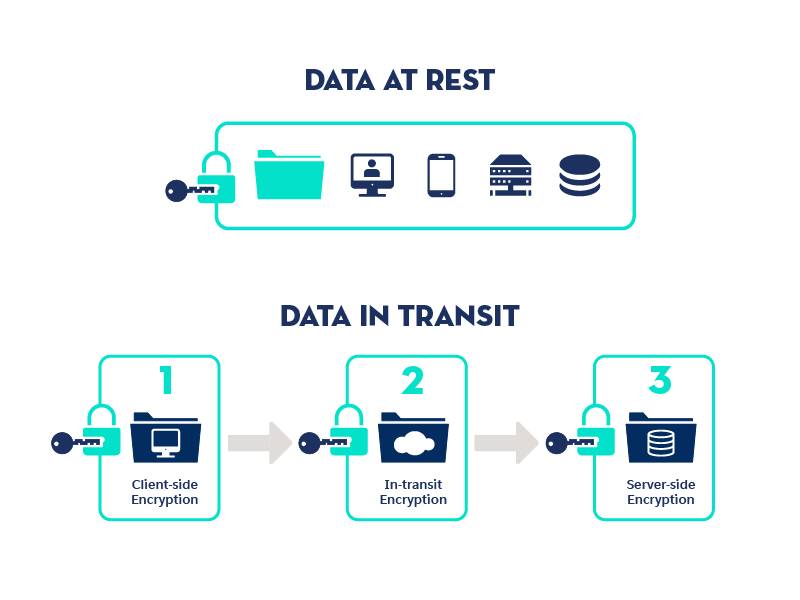
Data at rest refers to data stored on devices, while data in transit refers to data being transmitted over networks. To secure data in both scenarios:
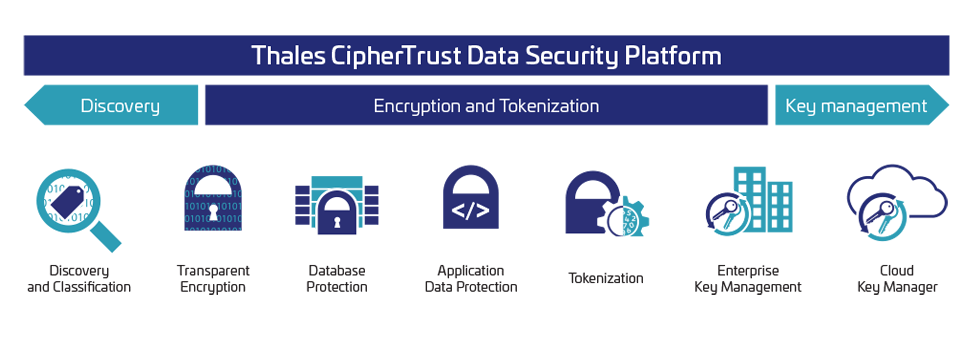
Managing Encryption Keys
Encryption keys are a critical component of data encryption. Proper key management involves:

- Key generation and distribution.
- Key storage and protection.
- Key revocation and rotation.
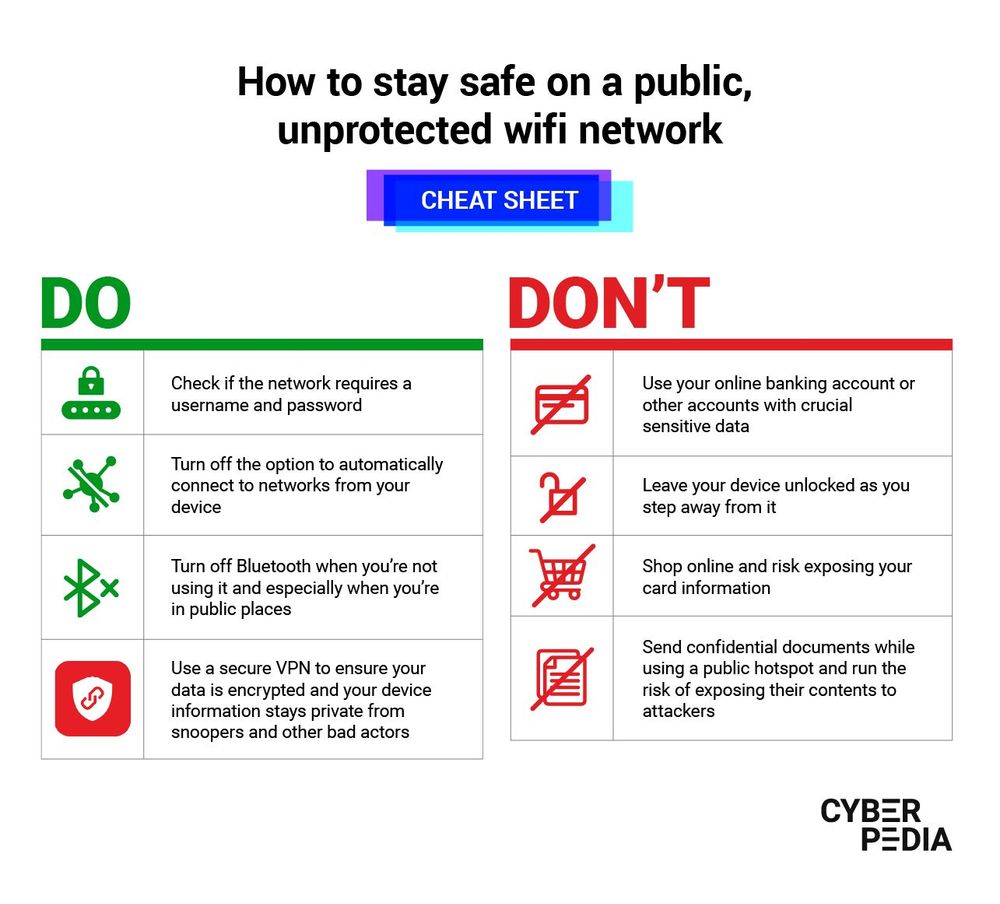
Implementing Secure Passwords
Passwords are a common entry point for unauthorized access. To secure passwords, use strong, unique passwords for each account, and consider implementing a password manager.
Encrypting Data on Mobile Devices
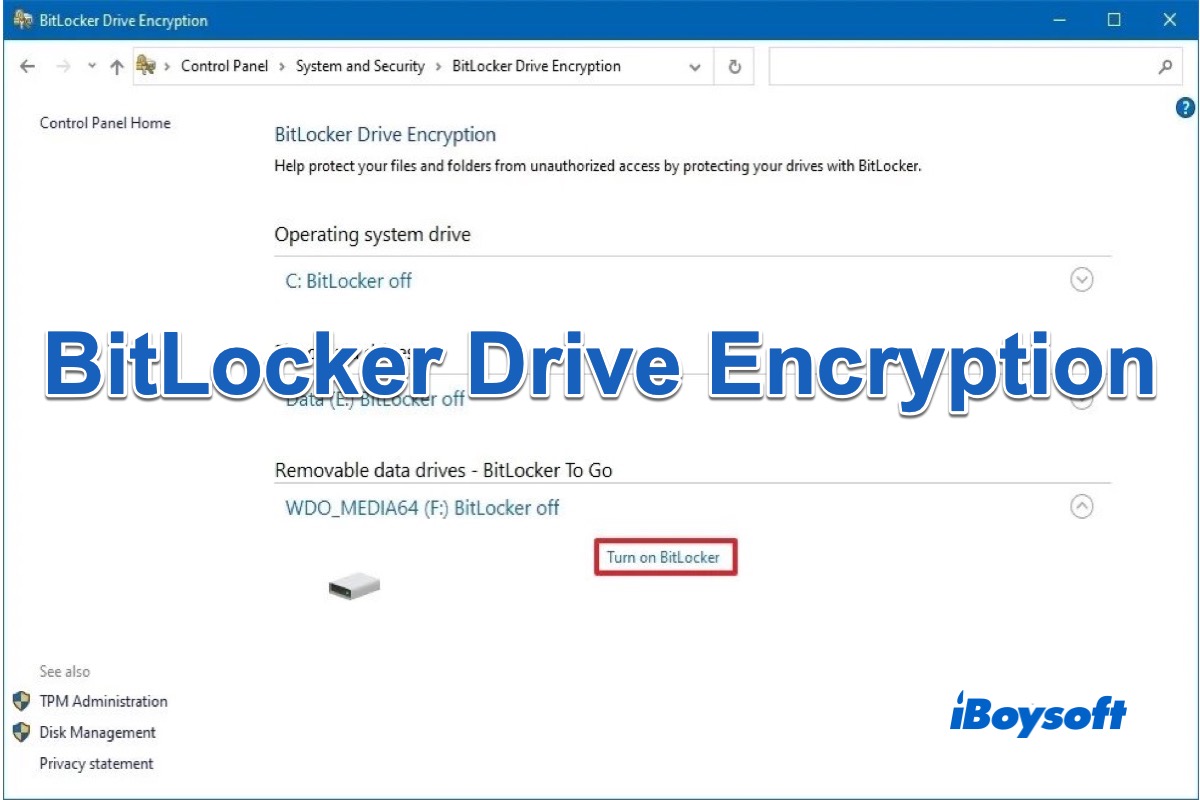
Mobile devices are a common target for data breaches. To secure data on mobile devices:
- Use full-disk encryption.
- Implement lock screens and biometric authentication.

As we can see from the illustration, How To Use Encryption To Protect Your Data has many fascinating aspects to explore.
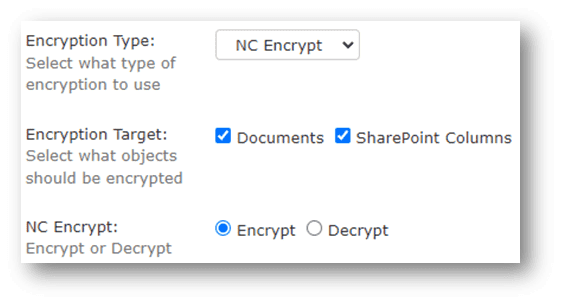
Cloud Data Encryption
Cloud storage presents unique data security challenges. To secure data in the cloud:
- Use cloud-based encryption solutions.
- Implement access controls and permissions.
Securing Email Communications
Email is a common vector for data breaches. To secure email communications:
- Use encryption protocols like PGP or S/MIME.
- Implement access controls and permissions.
Conclusion
Data encryption is a vital component of modern data security. By understanding the basics, types, and best practices of data encryption, individuals and organizations can protect sensitive information from unauthorized access. Remember to choose the right encryption algorithm, secure data at rest and in transit, manage encryption keys, implement secure passwords, and encrypt data on mobile devices and in the cloud. With these strategies in place, you can ensure the confidentiality, integrity, and availability of your valuable data.